terça-feira, 18 de janeiro de 2011
Advantages Of Remote Computer Entry Laptop or computer software
Technologies has forever altered our individual and operate lives. With accessibility to the newest personal computers and programs, it's achievable to total tasks quicker and a good deal much far more effectively than in the previous. Over the previous few years there has become a significant strengthen inside the number of individuals operating type residence on the total time or component time basis. This might be a way of life selection that's now less difficult thanks to remote Pc accessibility software system.
Possessing accessibility in direction of the information stored on a Computer from another place can enhance our operate and individual lives significantly. For example, if you truly feel under pressure to complete an critical project, being inside a position to log on for your office individual computer in the comfort and convenience of the personal residence can help to make particular that deadlines are met. All which you would demand is to have each PCs switched on and connected to the globe wide internet.
When you 1st open the remote Computer application you'll be prompted for your username and password of your personal computer you would like to create use of. As lengthy as each the PCs have been configured correctly, you will then be in a very position to log on to the remote Computer and use it as if it is your main workstation.
This application system is also of value if you're sick or compelled to get depart since of a family members difficulty. There would no longer be a must worry about not becoming able to keep track of vital work documents. You can just transfer data from 1 Computer to but another when it is needed.
It truly is not only your operate e mail account that you simply basically would be able to create use of from another Computer, any folders, files, and documents stored around the other individual computer will likely be available. If you have an curiosity in investing more time working from residence, this application may possibly nicely just be the reply you are looking for.
Every week a lot a lot a lot more of us pick to operate from our quite own homes as opposed to face a lengthy commute to an workplace. With fast broadband speeds now common place across most areas and districts, a lot of organizations are encouraging their workers to spend a while operating from house.
It's not just in the world of enterprise that remote Computer application plan can be employed to excellent impact. You'll be capable of also use the precise same applications to keep track of the goings-on in your very own house. For example, if you're at work and have left a variety of trades-people inside your residence to carry out repairs, it could be possible to accessibility your property Pc and check activities via the webcam.
The same application can also be useful in the home if you have children and are worried about their browsing activities. It is not always possible to physically sit with young kids to observe their online habits. With remote PC access software you can easily find out what websites have been visited and if any worrying downloads have been stored on the PC.
sexta-feira, 14 de janeiro de 2011
A Management Software Inventory System Saves Time And Negates Risk
There are very few companies that do not use desktops or laptops in todays competitive environment It is not uncommon to have a variety of operating systems and proprietary packages across a myriad of hardware platforms. If for no other reason than maintaining security, it is critical to keep a tally of what each user can access.
Most companies do not allow their staff to have access to all the levels a program may offer. For example, managers will have a higher level of access and other reporting tools than their direct reports will. Dependent on the departments needs, different tools will be used from accounting to graphics and everything in between.
Having this type of control allows the information officer to duplicate common features rapidly across multiple machines. With a mirror image of a machine, you can readily duplicate over to a machine that will be used by someone performing similar tasks. It also facilitates installation on new equipment or, in the event of hard disk loss, a new drive.
As providers are getting savvier at tracking their licenses, you run the potential of having unauthorized programs installed on your machines. With this type of system, you will know at a quick glance what is authorized and ensure you are compliant with licensing. Furthermore, you will have greater control over unauthorized alien ware.
Unless you build them yourself, your machines will come with an operating system already installed. However, updating these and creating customization can be time consuming if you need to sit at every machine. You will no longer need to do this, as you will be able to install any upgrades, hot fixes and more from a central environment.
With a clear knowledge of what you have and do not have, you will avoid an unneeded outlay of money for programs you may already have licensed and that are installed on machines that are no longer in operation. Frequently, a user installs a shareware version and then a purchase request is sent to acquire a complete system. Having a database of what you own and are not using allows you to avoid purchasing something you may already have.
Electronic data security is a full-time effort. Preventing unauthorized access is easier with this tool and you can significantly reduce the risk of your data being compromised. Any investment you make in prevention will pay for itself in a short amount of time.
If this is your first time acquiring a solution, look for one that is turnkey and ready to go. Larger corporations will also benefit from turnkey programs that can be tailored to their specific needs. The important thing is to begin. No matter the size of your entity, begin preparation now to have complete control with management software inventory. Doing so allows you to reduce your risk and remain competitive.
While it is not necessarily practical for the single user or small entrepreneurial business, it is always important to use a method to manage what is installed on your computer systems. Using a Management Software Inventory allows you to maintain everything you have installed in one centralized location. Although there are many tools available to achieve this goal, seek out a method that gives you plenty of room for future growth.
Nearly all companies rely on personal computers to perform multiple functions within their business. With many types of hardware and solutions, it makes sense to have a tool that allows the information department to know who has access to what, and control user access from a central point. Not only is this effective in data control, it provides a significant cost savings.
Not all employees will have access to all the programs a company may have. As an example, there may be supervisors who have access to certain programs that an hourly employee would never use. Furthermore, the configurations and access levels will differ between job functions.
Having a baseline image of installed programs on each piece of hardware is critical for the IT Department. This allows the IT professionals to restore programs in the event of data loss or other disaster, without significant downtime. When new equipment is acquired, this image can be moved quickly to facilitate the installation process.
As providers are getting savvier at tracking their licenses, you run the potential of having unauthorized programs installed on your machines. With this type of system, you will know at a quick glance what is authorized and ensure you are compliant with licensing. Furthermore, you will have greater control over unauthorized alien ware.
Most computers are going to have the basic operating systems and productivity tools preinstalled. Through controls designed to mitigate license issues, you will find the headache of tracking installed versions is virtually eliminated. It will also facilitate upgrades when they become available.
Another benefit from knowing exactly what is installed and available allows you to avoid purchasing packages for which you may already have licenses. You may find that individuals, who think they know what they are doing, will install shareware or other free versions of popular programs. They may then ask the purchasing agent to acquire the fully functional version. If the IT and Purchasing Departments communicate on such purchase orders, you will instantly see financial savings by not acquiring licenses you may already have.
Cyber security is becoming an ever-increasing priority in corporations. You will always be at risk. However, through expansive knowledge that is readily accessible, you will be able to avoid the loss of data and the potential for unauthorized access. Prevention far exceeds the cost of loss and recovery and if your data is sensitive, you will want to ensure you have complete control over who has access and how.
Whether you are starting from scratch or upgrading, be sure you keep your system current. Many solutions are available that can be customized to your exact requirements. It is imperative to maintain your database and keep it accurate. Regardless of the company's size, start now and avoid the potential for data loss through using a management software inventory system.
While sometimes impractical for the individual or small business, it serves to find a solution for any size business to track all their programs, associated licenses, and users. With Management Software Inventory, you will have an effective tool to manage all your installations in one convenient place. While there are several options available to do this, look for a solution that provides you room to grow as your business expands.
Nearly all companies rely on personal computers to perform multiple functions within their business. With many types of hardware and solutions, it makes sense to have a tool that allows the information department to know who has access to what, and control user access from a central point. Not only is this effective in data control, it provides a significant cost savings.
Not all employees will have access to all the programs a company may have. As an example, there may be supervisors who have access to certain programs that an hourly employee would never use. Furthermore, the configurations and access levels will differ between job functions.
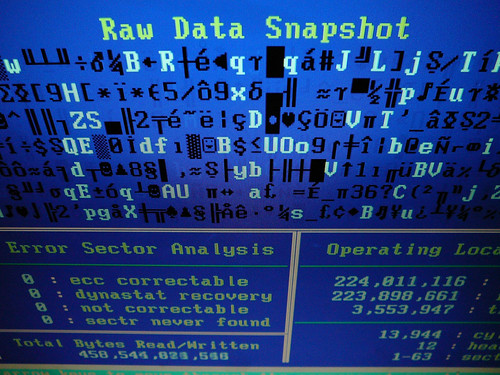
Having a baseline image of installed programs on each piece of hardware is critical for the IT Department. This allows the IT professionals to restore programs in the event of data loss or other disaster, without significant downtime. When new equipment is acquired, this image can be moved quickly to facilitate the installation process.
Another potential risk of not having a map is tracking licenses. Without knowing the number of licenses and running programs, there is a fiduciary risk to the company. Having no immediate record can also lead to a loss of control.
Most computers are going to have the basic operating systems and productivity tools preinstalled. Through controls designed to mitigate license issues, you will find the headache of tracking installed versions is virtually eliminated. It will also facilitate upgrades when they become available.
With a clear knowledge of what you have and do not have, you will avoid an unneeded outlay of money for programs you may already have licensed and that are installed on machines that are no longer in operation. Frequently, a user installs a shareware version and then a purchase request is sent to acquire a complete system. Having a database of what you own and are not using allows you to avoid purchasing something you may already have.
Cyber security is becoming an ever-increasing priority in corporations. You will always be at risk. However, through expansive knowledge that is readily accessible, you will be able to avoid the loss of data and the potential for unauthorized access. Prevention far exceeds the cost of loss and recovery and if your data is sensitive, you will want to ensure you have complete control over who has access and how.
If this is your first time acquiring a solution, look for one that is turnkey and ready to go. Larger corporations will also benefit from turnkey programs that can be tailored to their specific needs. The important thing is to begin. No matter the size of your entity, begin preparation now to have complete control with management software inventory. Doing so allows you to reduce your risk and remain competitive.
quinta-feira, 13 de janeiro de 2011
How To Buy The correct Internet Security Software For An Cost-effective Value
Most individuals in nowadays society very own a personal computer or perhaps a laptop computer. They also are likely to have an web connection therefore they could access the world broad web. Nonetheless, this inevitably brings up the dilemma of viruses along with other web associated potential risks. The answer for such points can be a software program that protects the computer. The suggestions in the subsequent paragraphs will inform 1 how to buy the best internet security software for an affordable value.
If one has never had a personal computer just before then he is possibly not really skilled on this subject. These folks are advised to speak to their household members and their buddies. Usually, a minimum of one or two of these men and women will know a whole lot about computer systems and virus safety.
Yet another choice is to go on the web and study this subject. In this case one will have to examine as many posts related to this subject as achievable. On the internet forums and chat internet sites will also support a person to get some good advice for his problem. One could also wish to think about to buy some Pc magazines and get additional data from there.
When considering of purchasing this product 1 will inevitably think of the price first. Once more, the planet extensive web can support a whole lot as you'll find many on-line comparison web pages that enable a person to find out the prices with the diverse software program and sellers. One has also got the option to buy the product on the web.
The other alternative is to drive about in one's city and visit all the shops and retailers that sell this kind of computer software. Although this can be far more time consuming and one has to invest some money on fuel, it really is really worth it as one cannot only talk towards the skilled shop assistants but also see the goods for himself. 1 should use this opportunity and get as significantly info through the store assistants as possible.
Following possessing checked the world wide web and the local stores 1 may well desire to transfer on and get one of your goods. On this case he can possibly order it on the web or go and gather it from shop. The benefit of ordering in the world extensive internet is the fact that one can possibly obtain the software program immediately or it'll be delivered to his house. Although this is really a very comfy choice, one has to watch for the publish to deliver the purchased item.
Buying it within a store is less comfortable as 1 has to drive to the shop, stand within the queue after which deliver the product property. Nevertheless, one does not have to wait two or 3 business days for the delivery to arrive. The customer is advised to maintain the receipt the purchase in case their are some troubles using the item later on.
Acquiring read the suggestions in the paragraphs over one should have a greater comprehension of how to purchase the best internet security software for an cost-effective value. Additional info can be discovered in Computer magazines or in articles published on the web.
Get inside information on how and where to purchase the right internet security software at a genuinely reasonably priced value now in our manual to leading safety computer software on http://it.n-able.com/
terça-feira, 11 de janeiro de 2011
Anti Virus Commander M
Anti Virus Programs
Anti-Virus software is crucial to your personal computer for numerous reasons. You'll find thousands and thousands of computer viruses and malicious packages on the internet. One can find also new ones being produced every day. These programmes may cause your computer (and you) hell. They might as well delete your data, broadcast your information to criminals, spy on all the details you do on the computer, use your computer to hack into a person else's computer, etc. You have spent a great deal of money in your new computer, so protecting yourself from all of these dangers is crucial!
It is probably one of several quicker of the anti-virus packages at scanning and eradicating any bothersome bugs on a users computer, and positively has some of the most colossal databases of bugs and viruses on the internet.
If your personal computer assumes form of contaminated by a virus package or attachment, you may not know it until you system seems to appearing up.
Listed beneath are a 9 main indicators that your PC may well be contaminated using a virus: Your PC seems to become running at a snail's pace.
AVG Anti-Virus Free V8
SuperAntiSpyware
MalwareBytes' Anti-Malware
Spybot Search and Destroy
First, uninstall your current anti-virus ever since it is not doing the occupation anyway. We are likely to be fitting a brand new anti-virus (AVG Anti-Virus Variation which you'll be able to start doing right now. Right after AVG 8 is installed and kept up to date please go forward and install the remaining 3 applications. Be sure to update each app following you put in it (each program has an replace menu or button).
Reboot your PC in safe mode (by tapping F8 in the course of your PC's startup). As soon as in safemode perform full scans using the 4 programs above (in that order). Quarantine anything looked at as an infection. Reboot. Your Rogue Anti-Virus has probably been removed along with the Trojans that downloaded it. If you are employing only IE7 or IE8 make sure you perform a reset on the browser as well.
Lots more revealed about anti virus here.
Elin Rehrig is our Anti Virus savant who also discloses information block email lotus notes,compare newegg,gaming barebone systems on their web site.
sexta-feira, 7 de janeiro de 2011
Access Remote Pc Secure Remote Access
Has it ever happened that you could not get to your PC and wanted something from it urgently? If this occurs to you frequently, there's a very favorable solution to steer clear of this from happening – Distant Access. As the phrase suggests, it means that you are able to access your PC from an inaccessible surroundings using only some other pc on the Web or LAN.
Work
There are several brands at the present that design Remote PC Access Software to help you connect to your computer easily and efficiently. Listed below are of the prominent ones:
PC remote access should be encrypted, and no one can easily "hack" in and see what type you are doing- not even the business that generates the service. Make sure the firm offers this of their features.
There are mixed look at when considering selecting just one among the many very many varieties of software programs available. The best action to take is to make use of any model that might work most suitable with the operating-system in the computer. Compatibility is the key problems before just one can even commence the entire process of accessing information from all of the locations.
Programs like VNC and pcAnywhere proliferated on the net with only basic user authentication, most times with weak passwords, as the security. Once hackers were capable of scan IP address ranges an "unpublished" IP postal address was just about useless for safety and of less value than the existing unpublished modem number.
Save Gas and Stress!- Rather than sitting in your particular vehicle for 2 hours a day in mind numbing traffic, why not sit down on your home PC and get many work done?
Bosses might have a happier work place- Give your staff members the freedom to get work carried out remotely and you will have your self a happier work force.
Lots more revealed about access remote pc here.
Walker Gebhart is this weeks Access Remote Pc specialist who also informs about monitor lizard,block email lotus notes,spyware doctor with antivirus on their blog.
Access Pc Remotely
Maintaining public entry PCs is extremely crucial. In areas similar to that of cyber cafes, hotels, libraries, universities etc. where computers are utilized by a number of individuals everyday, there’s the serious menace of misuse and sabotage. Suppose one of the users decides to end a banking transaction on one of several PCs and soon after, another consumer make up one's mind to steal the knowledge – it could be disastrous for the proprietor of the information. With impending identity theft threat wherever anything from credit card information, banking details, passwords, etc can be stolen, it turns into obligatory to have numerous sort of system that permits the network administrator to rollback the system to some other state that would not exhibit this delicate information. Rollback Rx system restore computer software and catastrophe restoration answer is a foolproof system that permits the administrator, with one click, to restore an entire network of PCs into the specified configuration.
Access Pc
The software programs is definitely very just like how many so-called spy ware packages work. You have a host laptop and an entry computer. By fitting a tiny piece of software on both computers, the entry computer may get complete management on the host. As scary because it might sound, this is actually very safe and a really highly effective way to supply complete versatility mobility.
What makes remote control access software programs so powerful it that it can give you complete control on the host PC. Its not just about connecting to check your e-mail or to repeat file or two across. Its similar to sitting at your work computer. It replicated your complete system which suggests that you can utilize the software programs on the host computer. You can certainly work, save files, print and also make use of the community - all from just one remote PC.
I am positive that you can start to see the would-be if you are an office employee who has to commute a lot. Since world-wide-web connections are practically with out limits these days, it permits you to entry your work laptop from everywhere in the world and at any time you would like without disrupting anything in your network.
If its flexibility you are looking for then that is a bit of computer software well worth investing in. In the event you are a company owner, then remote PC entry software can transform your company and provides you and your employees complete freedom and a much improved and really effective method communicate and collaborate.
To study more about remote PC entry software, visit my webpage and see which access computer software is appropriate for you.
Lots more revealed about access pc here.
Edie Payeur is this weeks Access Pc savant who also discloses strategies compare newegg,discount computer memory,gaming barebone systems on their web site.
quinta-feira, 6 de janeiro de 2011
Access Pc Software Access Software
Access Sfotware
Usually, the case would have been to report the criminal offense to the police and begin over with a brand new laptop. However this gentleman's case will end up being certainly one of a kind. With patience, perseverance, and a right option made prior to the laptop was stolen, he received it back. That choice was to utilize technologies known as remote control PC Access Software. He used the knowledge inputted by the laptop computer thief that the laptop computer owner acquired employing only this software, and he was able to follow the criminal and get back which sort was rightfully his with the assistance of the community police.
Packages such as GoToMyPC is incredibly simple to use and was produced with the home utilizer in mind. By basically installing the necessary computer software on 2 computers, you are capable of hook up with a number PC (like your computer at work) by way of a second computer just by using only an connection to the internet and an internet browser (like The net Explorer or Mozilla Firefox).
There was a time that such computer software was too complex to use for mass production. Today, drastic adjustments and enhancements to these packages not simply made them affordable, but in addition user-friendly to individuals who solely have common information and experience with computers. Teachers, businessmen, medical-related practitioners and scholars can easily now use remote control access PC software for fast information exchange and access. You need not have a bachelor's degree in computer science just to use this tool; purchase, download, and a quick read on directions is likely to make this computer software your chum in times of need.
So keep this in your mind when you are losing time in your companies computers. You might never know if they're watching your card entertainment or speaking to your boyfriend or girlfriend in an instant messenger. It could seem perfectly guiltless to you but to your business it may seem like some other subject all jointly and that is the concern that you ought to know about.
Discover more about access pc software here.
Cyrstal Dutta is our current Access Pc Software specialist who also informs about discount computer memory,sony laptops reviews,block email lotus notes on their site.